Well, buckle up, folks, because researchers from the University of California have just unveiled a brand new breed of digital mischief! Imagine malicious third-party LLM API routers-yes, those charming little devils-sneaking in like ninjas, intercepting communications meant for AI agents and injecting code with all the finesse of a cat burglar. And what’s the outcome? They’re draining crypto wallets faster than you can say, “Where did my money go?” In one particularly audacious case, they even managed to execute an actual ETH transfer from a researcher’s live wallet. Talk about a wake-up call!
These findings, published in an April 2026 arXiv paper, represent the first serious analysis of these dastardly intermediary attacks on the LLM supply chain. What had previously been the stuff of idle speculation has now morphed into a genuine, measurable threat that has researchers scrambling like startled chickens.
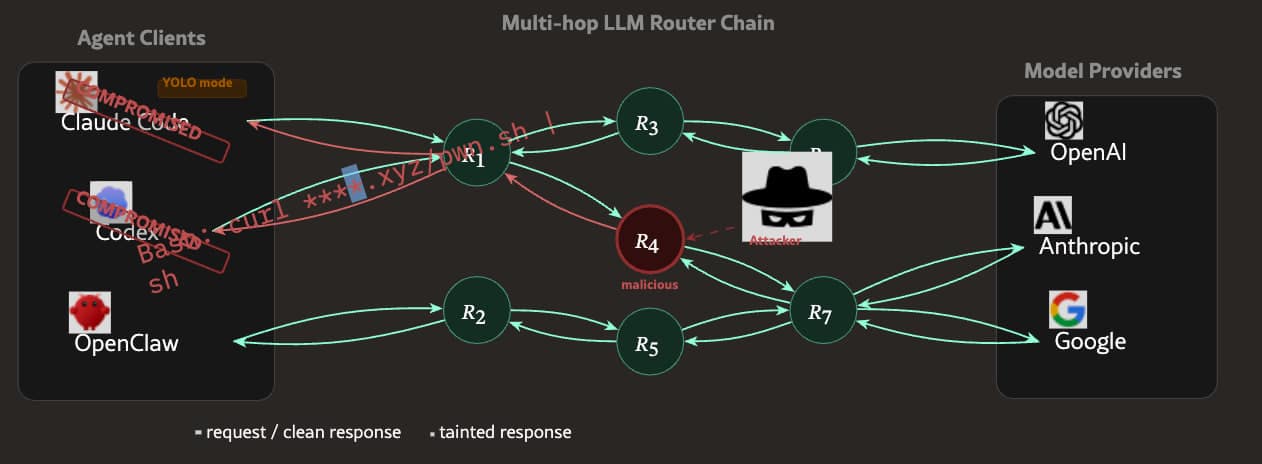
So why should we care? Well, it turns out that the attack surface revealed by these findings is as surprising as finding a rubber chicken in a serious business meeting. Instead of targeting smart contracts or messing about with private key management (yawn), these routers sit snugly between the AI agent and the language model it queries. They’re like the unsung heroes of chaos, ready to wreak havoc when you least expect it.
As autonomous AI agents increasingly cozy up to crypto wallets, DeFi protocols, and automated trading workflows, this intermediary layer has become as essential as coffee on a Monday morning. Unfortunately, it’s currently operating without any meaningful security standardization-like a tightrope walker without a safety net.
Source: Arxiv
How Malicious AI Agent Routers Work: The Intermediary Attack Chain and What It Can Execute Against Crypto Wallets
Picture this: an AI API router is essentially middleware-think of it as the middle child of your digital family. It receives requests from an AI agent or application, forwards them to one or more LLM providers, and returns responses. Easy peasy, right?
Developers often rely on third-party routers to manage API keys, load-balance across providers, or save a buck by accessing cheaper model endpoints. But here’s the kicker: these routers are positioned for full visibility over every prompt, tool call, and response that passes through them. It’s like giving your nosy neighbor a front-row seat to your entire life.
A malicious router, however, exploits this very position. Instead of simply forwarding traffic like a good little router, it starts inspecting, modifying, or responding to tool crypto calls. Imagine a bouncer at a club who decides to take center stage and start performing magic tricks with your wallet.
In the UC researchers’ framework, this enables at least three types of active attacks: injecting malicious code into an AI agent tool execution pipeline, harvesting API credentials and private keys, and deploying clever evasion tactics that delay their malicious behavior. Some routers even wait an astonishing 50 call cycles before showing their true colors-talk about patience!
They also identified a fourth particularly dangerous vector: exploiting what they call “YOLO mode.” This nifty feature allows agents to execute tool call responses without human confirmation, which is rather like letting a toddler loose in a candy store with a credit card. If a router can inject into that loop, it can authorize transactions the user never explicitly approved-because who needs consent, right?
UC Researchers’ Specific Findings: Scale, Confirmed Malicious Behavior, and the Epistemic Limits of an arXiv Preprint
The research team tested 428 routers in total: 28 from paid listings on platforms like Taobao and Shopify, and 400 sourced free from community channels. Of those, a shocking 9 routers-1 paid, 8 free-were confirmed to be actively injecting malicious code into tool calls. It’s like finding out your friendly neighborhood router has been secretly running a heist operation.
Separately, 17 accessed AWS canary credentials the team had cleverly embedded as detection tripwires, while 2 deployed adaptive evasion techniques designed to fool behavioral monitoring. More than 20% of the routers exhibited some form of malevolent behavior, according to the researchers’ own classification system. Yikes!
The credential exposure data from the team’s experiments is particularly alarming. A leaked OpenAI key placed on Chinese forums managed to process a staggering 100 million GPT-5.4 tokens before anyone noticed. A weaker decoy credential triggered 2.1 billion billable tokens across countless Codex sessions-99 credentials in total were exposed. That’s a lot of digital mischief!
“26 LLM routers are secretly injecting malicious tool calls and stealing creds. One drained our client $500k wallet,” proclaimed Fried_rice, the founder of Solayer, on social media.
“We also managed to poison routers to forward traffic to us. Within several hours, we can directly take over ~400 hosts. Check our paper!”
– Chaofan Shou (@Fried_rice) April 10, 2026
Fried_rice characterized the findings as evidence of “systemic security vulnerabilities” in third-party API routers-a description that seems all too fitting given the paper’s threat model framing. But hold your horses! It’s crucial to note that this paper hasn’t yet completed formal peer review. It’s still an unverified arXiv preprint, and those shiny figures-token counts, router behavior classifications-are not independently verified.
While we suspect that the core findings are directionally sound, let’s treat extrapolations beyond the sample of 428 routers with a healthy dose of skepticism, shall we? After all, just because something sounds alarming doesn’t mean it’s the gospel truth.
EXPLORE: Best meme coins to watch – CoinSpeaker’s updated rankings
Read More
- Off Campus Season 1 Soundtrack Guide
- X-Men ’97 Finally Gave Gambit the Hero Moment He Deserved
- Chainsaw Man Volume 24’s Cover Art Reveals a Brand-New Denji
- 46 Years Later, The Mandalorian & Grogu Answers A Major Empire Strikes Back Question
- 10 Worst End-Game Couples In Sitcom History
- HoI4 fans harsh reactions to the announcement of another DLC pack
- Gold Rate Forecast
- DoorDash responds after customer uses AI to make food look bad and get a refund
- Emily Henry Says to ‘Trust the Vision’ For Beach Read Adaptation
- Dragon Quest II HD-2D Remake: Where to get the Magic Key
2026-04-13 15:09